With the growth in the cyberattacks many companies are taking innovative route to keep vulnerability at a bay and there is a good traction of zero trust adoption among the enterprises to strengthen the security posture
India is facing an unprecedented increase in cyberattacks—in the first three months of 2022, India witnessed 18 million cyberattacks and threats, an average of 200,000 attacks every day, according to US based cyber security firm, Norton.
What is worrying is that India Inc badly needs a refresh of the cyber security approaches and technologies currently being employed. According to a study by Cisco 37% of the cyber security technologies used by companies in India are considered outdated by cyber security and privacy professionals working in these organizations.
The cyber security trends in India are in tandem with global experiences and this is evident in the Gartner 2021 CIO agenda survey which indicates cybersecurity as the top priority for new spending amongst 61% of CIOs.
As more organizations leverage cloud computing, the traditional network security perimeter has all but vanished, and security teams are finding it difficult to identify who and what should be trusted to allow access to the networks. Perimeter network security focuses on keeping attackers out of the network but this traditional approach is vulnerable to users and devices inside the network.
According to Forrester Research, an estimated 80% of breaches involve privileged access abuse. Such violations include highly visible supply chain breaches at Solar Winds, Microsoft Exchange, and Colonial Pipeline which have brought zero trust into the spotlight.
VPNs which were traditionally employed to grant remote access today are cumbersome and do not provide the level of security anymore. Zero Trust is an approach to secure the entire infrastructure with a range of strategies that are designed for breach. Nobody is trusted automatically, even after clearing the perimeter—instead all identities are verified, minimum access is granted based on context, and activities are monitored to make sure controls are working as expected.
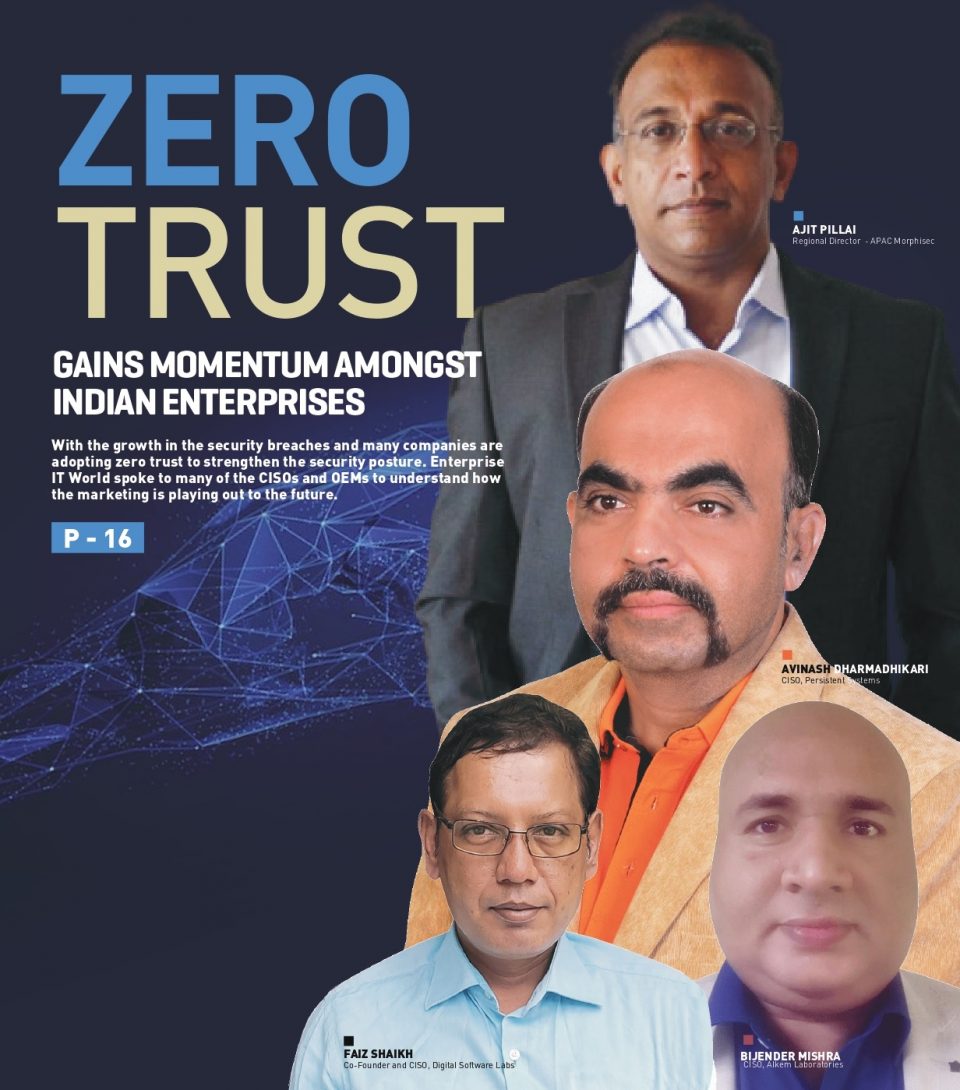
“Limiting access as much as possible while verifying anything given access is at the heart of zero trust. This approach can be applied in all facets of cybersecurity so that attacks must overcome repeated obstacles and evade constant scrutiny,” Ajit Pillai, Regional Director -APAC, Morphisec.
The increasing use of people inside the perimeter via phishing, vulnerable email attachments and poisoned URLs means that more often the attack effectively begins from inside the safe space. Zero trust approach addresses this concern rejecting the assumption that the inside of your perimeter is a safe space to an assumption that nobody within or outside the environment can be trusted. As restricted corporate networks become more vulnerable to cyberattacks and remote access becomes the norm rather than the exception, the once tried-and-tested security methods have been losing relevance.
“Amidst this, the zero-trust approach to security, which reduces the risk of data exfiltration, provides protection against a wide range of threats and offers users a smooth and secure experience. Zero trust is seeing increased adoption particularly in an environment that is no longer limited to the confines of the traditional office network,” says Avinash Dharmadhikari, Chief Information Security Officer at Persistent Systems.
“The zero-trust approach to security reduces the risk of data exfiltration, provides protection against a wide range of threats and offers users a smooth and secure experience. Zero trust is seeing increased adoption particularly in an environment that is no longer limited to the confines of the traditional office network.”
Avinash Dharmadhikari, CISO, Persistent Systems
Zero Trust Approaches Gaining Momentum
According to Cisco’s “Security Outcomes Study Volume 2, zero-trust approaches have penetrated well into Indian organizations with nearly nine in 10 (89 per cent) respondents in India said the company is investing in a ‘Zero Trust’ strategy, with 44 per cent making steady progress in adoption and 45 per cent are at a mature state of implementing it.
Says Bijender Mishra, CISO, Alkem Laboratories Ltd, “We were the first pharma company in India, implemented ZT and it helped us to reduce business and organizational risk; better control access to Cloud and container environments; and achieve continuous compliance requirements.”
Adds Avinash, “We are gradually moving towards zero trust. As a software development firm doing a full zero trust implementation comes with unique challenges but it is an evolving process and we have to carry along all stakeholders.”
The rapidly evolving IT landscape with Cloud-first and mobile-first approach along with the pandemic that required organizations to extend the corporation to the homes of employees expanded the surface area of attack. This created complex IT environments that are spread across corporate data centers, co-location centers and public Cloud enlarging the space for defenders to protect.
As more organizations do more computing outside their perimeter in the cloud, security teams find it increasingly difficult to trust or identify who and what should be allowed or trusted with access to their networks.
“Zero Trust simply starts on the principles of trusting no one and least privilege, thereby it enforces something beyond standards and frameworks. Even if any organization gets breached, logically the attacker would use privilege escalation in the next step but zero trust is designed to prevent the next step for any attacker,” says Faiz Shaikh, Co-Founder and CISO, Digital Software Labs.
Given the complexity of the technology environment specifically as public Cloud comes into play, old approaches of securing the perimeter are no longer sufficient and organizations have to find new ways of enhancing security systems with new approaches such as least privilege access or zero-trust which require every user and device to be authorized and authenticated at each layer.
All companies need to move security forward to ensure that they can rapidly identify threats and quickly respond. Zero trust frameworks, when implemented well, can help to protect organizations from unauthorized access to networks, applications, and data. Granular access to resources ensures more control within the network and restricts the damage a breach can cause.
User and device authentication is a key pillar of organizational security and all users, both inside and outside the network, must be validated at each layer for higher security. The environment is continuously monitored via tools that provide high level of visibility into who is accessing what. In case of breach, the system sends an alert and resolution is quickly achieved with log tracing.
“Once in place, the Zero trust model better secures the company, especially from in-network lateral threats that could manifest under a different security model. It entails strong management of users inside the network, multi-factor authentication or even moving beyond passwords with biometrics, and categorization of users—all of which strengthens the security system of the organization,” says Bijender.
“Zero Trust simply operates on the principles of trusting no one and least privilege, thereby it enforces something beyond standards and frameworks. Even if any organization gets breached, logically the attacker would use privilege escalation in the next step but zero trust is designed to prevent the next step for any attacker.”
Faiz Shaikh, Co-Founder and CISO, Digital Software Labs.
Primary elements of a zero-trust security architecture
The Zero Trust model requires multiple security controls throughout an IT environment to protect and manage identities, devices, networks, applications, and data. The single largest aspect of a Zero Trust architecture is the concept of identity and this includes establishing identity (authentication) and the assignment of privileges to the identity (authorisation). Zero Trust, as the name indicates, focuses on verifying and validating identity rather than blindly trusting prior authentication and authorisation.
Speaking about zero-trust implementation, Bijender, says, “Adding security parameters to existing applications to make them zero trust-aware is not always feasible. Odds are your existing applications have no facilities today to accommodate zero trust. Therefore, depending on what kind of custom applications you have will dictate whether or not you can adopt zero trust to those processes, and potentially determine the effort and cost required. This is especially true when applications are not microperimeter-compatible, or where no API is exposed to support the required automation.”
While there are many starting points on the path to zero trust, all roads still lead to identity, with privileged access controls being the lowest-hanging fruit. With an identity-centric zero-trust approach, organizations can ensure least privilege access by verifying who or what is requesting access, the context of the request, the risk to the access environment, and just-in-time/just enough privilege elevation.
Zero Trust views every attempt to access the network as a threat. While traditional security often requires nothing more than a single password to gain access, multi-factor authentication (MFA) requires users to enter a code sent to a separate device, such as a mobile phone, to verify they are in fact who they claim to be. The objective is to prevent unauthorized access to data and services and make control and enforcement as granular as possible.
Privileged Access Management (PAM) capabilities such as verifying identities, MFA, and enforcing least privilege makes zero trust a robust security model.
Referring to the NIST 800-207 recommendations, Avinash Dharmadhikari, CISO, Persistent Systems, emphasizes continuous verification to always verify access, all the time, for all resources. The second thing is to limit the “blast radius” and minimize impact if an external or insider breach does occur. And thirdly, automate context collection and response so you can incorporate behavioural data and get context from the entire IT stack (identity, endpoint, workload, etc.) for the most accurate response.
“Adding security parameters to existing applications to make them zero trust-aware is not always feasible. Odds are your existing applications have no facilities to accommodate zero trust. Therefore, depending on the kind of custom applications will dictate whether or not you can adopt zero trust to those processes, and potentially determine the effort and cost required.”
Bijender Mishra, CISO, Alkem Laboratories
Balancing Zero Trust with Business Priorities
Zero Trust is not a technology, it’s an architecture and as such is made up of many components, most of which are not dependent on each other. The implementation cannot be achieved via a big-bang approach, rather it is a journey with manageable steps that must be taken one at time.
A key challenge of zero trust implementation is that it must be delicately balanced with business priorities for effective outcomes. Otherwise, it can slow down business processes and affect productivity which in turn will lead to greater challenges as employees start finding ways to circumventing the security system.
As zero-trust models rely on a vast network of strictly defined permissions, effective implementation require a large amount of administrative responsibilities. Businesses and companies are in a dynamic mode and people are often moving into new roles or changing locations and keeping the permissions accurate and up to date requires ongoing input and considerable management effort.
Even as things change inside the organization, people require continuous and consistent access to sensitive data and information to work, communicate and collaborate and so access controls must be updated each time to ensure the correct people have access to specific information.
“Zero-trust models rely on a vast network of strictly defined permissions, but companies are always evolving. People move into new roles and change locations. Access controls must be updated each time to ensure the correct people have access to specific information. Keeping the permissions accurate and up to date requires ongoing input.” says Avinash.
Further, Dharmadhikari states that this can become problematic if controls aren’t updated immediately as unauthorized parties could gain access to sensitive information. For instance, an employee that has been fired and can still access internal information, is a vulnerable state for the organization as the employee can turn rogue and expose data.
“Employee need to be monitored more closely and access must be granted according to the profile of the user. Today’s work environment includes not only different kinds of users, but several types of devices and different devices may have their own properties and communication protocols which must be monitored and secured specific to their type,” says Bijender.
The process of delivering Zero Trust is also going to unlock many of the regulatory compliances, or at least the cybersecurity aspects of them, that companies have to address now or in the future. When you are implementing an architecture assembled from foundational cybersecurity practices, that foundation provides the base for more than just the architecture itself.
“Limiting access as much as possible while verifying anything given access is at the heart of zero trust. This approach can be applied in all facets of cybersecurity so that attacks must overcome repeated obstacles and evade constant scrutiny.”
Ajit Pillai, Regional Director -APAC, Morphisec.
The Outlook
Embracing zero-trust puts cyber security in the front and center of organizational strategy. Business operations are closely integrated with technology systems and these systems are under constant attack from threat vectors. Organizations must shift the mindset from “How do we implement this and secure it?” to “How do we securely implement this?” Given that businesses operate in a dynamic environment, the security posture also needs to evolve and adapt continuously to mitigate cyber security risks and enhance business resilience.