IptabLes and IptabLex infections on Linux systems, large and growing botnet believed to be expanding from Asia to more regions
Akamai has released, through the company’s Prolexic Security Engineering & Research Team (PLXsert), a new cyber security threat advisory. The advisory alerts enterprises to a high-risk threat of IptabLes and IptabLex infections on Linux systems.
Malicious actors may use infected Linux systems to launch distributed denial of service (DDoS) attacks against the entertainment industry and other verticals.
“We have traced one of the most significant DDoS attack campaigns of 2014 to infection by IptabLes and IptabLex malware on Linux systems,” said Stuart Scholly, senior vice president and general manager, Security Business Unit, Akamai. “This is a significant cyber security development because the Linux operating system has not typically been used in DDoS botnets. Malicious actors have taken advantage of known vulnerabilities in unpatched Linux software to launch DDoS attacks. Linux admins need to know about this threat to take action to protect their servers.”
Command and control centers (C2, CC) for IptabLes and IptabLex are currently located in Asia. Infected systems were initially known to be in Asia; however, more recently many infections were observed on servers hosted in the U.S. and in other regions. In the past, most DDoS bot infections originated from Russia, but now Asia appears to be a significant source of DDoS development.
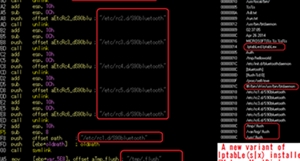
Detecting and preventing an IptabLes or IptabLex infestation on Linux systems involves patching and hardening Linux servers and antivirus detection. In the threat advisory, PLXsert provides bash commands to clean an infected system.
DDoS mitigation for the target of a DDoS attacker who controls these infected bots may include rate-limiting DDoS mitigation techniques. In addition, PLXsert shares a YARA rule in the threat advisory to identify the ELF IptabLes payload used in an observed attack campaign.